Видео с ютуба Security Policy Education

Security Policies - CompTIA Security+ SY0-701 - 5.1

Why Consider Sanford's Master of National Security Policy? | Sarah Blake MNSP'24

Lock Down Your Microsoft 365: Your Essential Security Policies

Security Policy | SUBJECT: CSA23103

Stupid School Security and Discipline Policies | Jennie Young | TEDxUWGreenBay

How to write an IT security policy - Comprehensive guide with free template - 2025
Security Policy Studies

Information Security Policy (CISSP Free by Skillset.com)

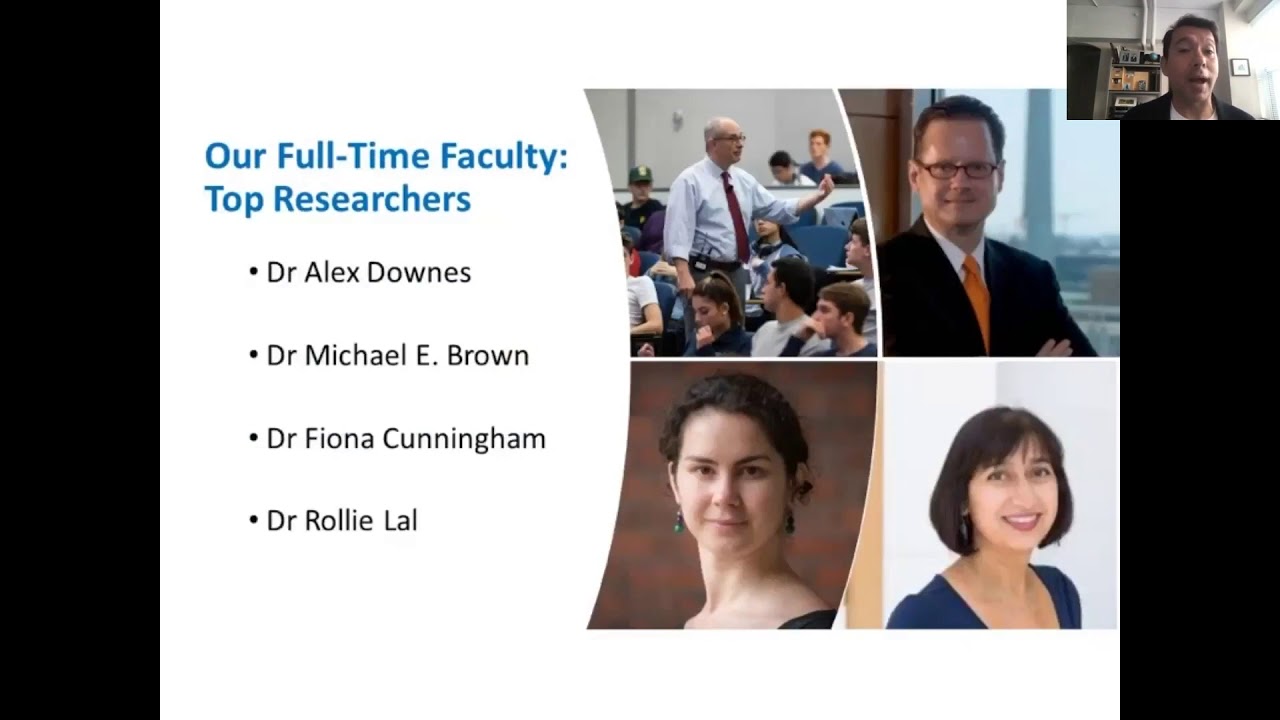
Security Policy Studies (SPS) at the Elliott School

How to Write INFORMATION SECURITY POLICY | What is information security policy | IT security policy

Зачем изучать политику национальной безопасности?

How to create an Information Security Policy in under 5 minutes

Information Security Awareness Employee Training: Protect Your Company's Data and Reputation

Security & AI Governance: Reducing Risks in AI Systems

Cybersecurity Architecture: Five Principles to Follow (and One to Avoid)

How to write an Information Security Policy inline with ISO 27001

What Is Cyber Security | How It Works? | Cyber Security In 7 Minutes | Cyber Security | Simplilearn

3.1 Security policy and standards

Security Policy Training and Procedures - CompTIA Security+ SY0-401: 2.6

Introducing the Sanford School's Master of National Security Policy Program